The post Keeping Kids Safe: A Detailed Guide on How to Setup Parental Controls on Android Devices appeared first on gadget.apola.co.
]]>This article delves into the various methods available for configuring parental controls on Android devices. We will explore the native Google Family Link app, a powerful and free tool that allows parents to monitor and manage their child’s device usage, app activity, and screen time. Furthermore, we will discuss alternative third-party applications, offering a range of functionalities to suit different parenting styles and needs. Regardless of your technical expertise, this guide is designed to be easily understood and implemented. Our primary goal is to equip parents with the knowledge and tools necessary to create a secure and age-appropriate digital environment for their children, promoting responsible digital citizenship and mitigating the potential harms associated with unrestricted online access.
Understanding the Importance of Parental Controls
In today’s digital age, children have unprecedented access to a vast amount of online content. While the internet offers numerous educational and entertainment opportunities, it also presents potential risks that necessitate the implementation of parental controls.
Parental controls are crucial for safeguarding children from exposure to inappropriate content, cyberbullying, online predators, and excessive screen time. These tools empower parents to actively manage their child’s online experience and foster a safer digital environment.
Without proper supervision, children are vulnerable to:
- Accessing explicit or violent material.
- Engaging in risky online behaviors.
- Developing unhealthy screen time habits.
- Becoming victims of cybercrime.
By understanding and utilizing parental controls, parents can proactively mitigate these risks and ensure their children’s safety and well-being in the digital world.
Setting Up Google Family Link for Parental Supervision
Google Family Link is a powerful tool provided by Google to help parents supervise their child’s Android device. This setup process involves linking the parent’s Google account with the child’s account, enabling parental controls.
Here’s how to get started:
- Download and Install: Download the Google Family Link app on both the parent’s and child’s devices from the Google Play Store.
- Create a Child Account: If your child doesn’t have a Google account, you’ll need to create one for them through the Family Link app. If they have an existing account, you can supervise it with parental consent.
- Linking Accounts: Follow the prompts within the app to link the parent and child accounts. This will involve entering codes and confirming the connection on both devices.
- Granting Permissions: Grant Family Link the necessary permissions to monitor app usage, location, and other relevant data.
- Review and Adjust Settings: Once the accounts are linked, you can begin customizing the parental control settings according to your child’s needs and your preferences.
Ensure you have physical access to both the parent’s and the child’s devices during the setup process for a smooth and secure configuration.
Managing App Downloads and Purchases
One of the crucial aspects of parental controls is managing app downloads and purchases. This involves preventing children from downloading inappropriate apps or making unauthorized purchases.
Restricting App Downloads
To restrict app downloads, access the Google Play Store settings through the Family Link app. Within the settings, you can configure the options to:
- Require parental approval for all downloads.
- Only allow downloads of apps appropriate for their age.
- Block specific apps entirely.
Managing In-App Purchases
In-app purchases can lead to unexpected charges. To manage this, ensure that purchase approval settings are enabled. This will require your permission before any in-app purchases can be made, effectively preventing accidental or unauthorized spending.
Payment Method Configuration
It’s important to review and manage the payment method associated with your child’s account. You can:
- Remove your credit card information from the account.
- Require authentication for every purchase.
Controlling Screen Time and Bedtime Schedules
Establishing healthy digital habits is crucial for children’s well-being. Parental control features on Android devices allow parents to manage screen time and set consistent bedtime schedules, promoting better sleep and balanced activities.
Google Family Link provides tools to set daily screen time limits for each child’s device. These limits can be customized based on the day of the week, allowing for flexibility during weekends or holidays.
Bedtime schedules can also be configured through Family Link. This feature automatically locks the device at a designated time, preventing usage during sleep hours. A friendly reminder is sent to the child before the device locks, encouraging them to wind down.
Parents can also grant bonus screen time in special circumstances. This provides a degree of flexibility while maintaining overall control.
Filtering Content and Blocking Inappropriate Websites
Protecting children from inappropriate online content is a crucial aspect of parental controls. Implementing filters and blocking mechanisms helps ensure a safer browsing experience on Android devices.
Utilizing Google SafeSearch
Google SafeSearch is a tool that filters explicit results from Google search. Enable it in the Google app settings and on other search engines your child might use.
Employing Website Blocking Features
Several parental control apps offer website blocking features. These allow parents to create blacklists of websites their children cannot access. Consider using these apps to block known sources of harmful content.
Leveraging YouTube Restricted Mode
YouTube Restricted Mode filters potentially mature content. Activate it within the YouTube app settings to minimize exposure to inappropriate videos.
Content Filtering Apps and Extensions
Explore third-party apps and browser extensions that specialize in content filtering. These tools often provide granular control over the types of content allowed on the device.
Monitoring App Usage and Activity
Effective parental control extends to monitoring how your child uses apps on their Android device. This involves tracking which apps are used most frequently and the duration of usage.
Benefits of Monitoring App Usage
Monitoring app activity helps parents understand their child’s interests and identify potential issues. It can also reveal if a child is using inappropriate apps or spending too much time on certain activities.
How to Monitor App Usage with Google Family Link
Google Family Link provides tools to view app activity. Parents can see a report of which apps their child uses and how long they spend on each app. This data is accessible through the Family Link app on the parent’s device.
Taking Action Based on Monitoring
Based on the app usage data, parents can make informed decisions. This may include blocking certain apps, setting time limits, or having conversations with their child about responsible app usage.
Setting Location Tracking for Child Safety
Ensuring your child’s safety extends to knowing their whereabouts. Location tracking, when implemented responsibly, can offer peace of mind and provide a valuable tool in emergency situations. Google Family Link allows parents to track their child’s Android device location.
Enabling Location Sharing
To activate location tracking, navigate to the Family Link app on your device. Select your child’s profile. Locate the “Location” card and ensure location sharing is turned on. Your child’s device must also have location services enabled.
Understanding Accuracy and Limitations
It’s important to understand that location tracking relies on GPS and cellular data. The accuracy of the location displayed can vary depending on signal strength and environmental factors. Remind yourself and discuss with your child that this feature is in place to increase their safety.
Respecting Privacy and Trust
Transparency is crucial. Discuss with your child why you are enabling location tracking and how it will be used. Emphasize that it’s a safety measure and not a tool for constant surveillance. Open communication will build trust and ensure your child understands the purpose of this feature.
Customizing Parental Control Settings for Each Child
Recognizing that each child has unique needs and maturity levels is crucial when implementing parental controls. A one-size-fits-all approach may not be effective. Customization allows for a more tailored and appropriate digital environment for each individual.
Age-Appropriate Settings
Consider the child’s age and developmental stage when adjusting settings. Younger children might require stricter content filtering and screen time limits, while older children may benefit from more autonomy with increased responsibility.
Individual App Permissions
Grant or restrict access to apps based on each child’s needs and interests. Some apps may be beneficial for educational purposes or creative expression, while others may be unsuitable. Regularly review app permissions and make adjustments as needed.
Communication and Collaboration
Involve your children in the process of customizing parental controls. Openly discuss the reasons behind certain restrictions and listen to their concerns. This collaborative approach fosters trust and encourages responsible online behavior.
Discussing Online Safety with Your Children
Open communication is paramount in ensuring your child’s safety online. Parental controls are vital tools, but they are not a substitute for direct conversations about the potential dangers and responsible online behavior.
Start by establishing a safe and supportive environment where your child feels comfortable discussing their online experiences. Explain the risks of sharing personal information with strangers, the importance of cyberbullying prevention, and the potential exposure to inappropriate content.
Emphasize the permanence of online posts and the significance of digital reputation. Encourage your child to think critically about the content they consume and share online. Regularly engage in conversations about online safety, adapting your approach as your child grows and their online activities evolve.
Here are some key talking points:
- Privacy Settings: Explain how to adjust privacy settings on social media platforms and apps.
- Stranger Danger: Reinforce the dangers of communicating with strangers online.
- Cyberbullying: Discuss what cyberbullying is and how to report it.
- Inappropriate Content: Explain the types of content to avoid and how to handle accidental exposure.
Alternative Parental Control Apps for Android

While Google Family Link is a robust option for parental controls, several alternative apps offer unique features and benefits. Exploring these alternatives can help you find the perfect fit for your family’s specific needs.
Popular Alternatives:
- Qustodio: Offers comprehensive monitoring, including social media activity and call/SMS tracking.
- Norton Family: Provides web supervision, time supervision, and location supervision.
- Kaspersky Safe Kids: Includes features like GPS tracking, safe search, and YouTube monitoring.
- Bark: Specializes in detecting signs of cyberbullying, depression, and suicidal thoughts.
When choosing an alternative app, consider factors such as: features offered, ease of use, pricing, and compatibility with your devices. Always research and read reviews before committing to a particular app to ensure it aligns with your child’s age and your parenting style.
The post Keeping Kids Safe: A Detailed Guide on How to Setup Parental Controls on Android Devices appeared first on gadget.apola.co.
]]>The post Unlock Your Device’s Secrets: A Detailed Guide on How to Find Your iPhone Serial Number Easily appeared first on gadget.apola.co.
]]>From the latest iPhone 15 to older models, the process of retrieving your serial number is usually straightforward. Our guide will explore multiple methods, including checking your device settings, using iTunes or Finder on your computer, and even examining the physical device itself. This information is important for international readers because serial numbers are universal identifiers that enable access to support and services, regardless of geographical location. Learn how to quickly and effortlessly retrieve this important data and unlock a wealth of information about your iPhone.
Understanding the Significance of Your iPhone Serial Number
The serial number of your iPhone is a unique identifier assigned to your specific device by Apple. It is essential for various purposes, acting as a digital fingerprint that distinguishes your iPhone from all others.
Why is this number so important? Think of it as your iPhone’s passport. It allows Apple and authorized service providers to:
- Verify warranty status: Determine if your device is still under warranty.
- Track repair history: Access records of any past repairs or services.
- Authenticate your device: Confirm the iPhone’s legitimacy and prevent fraud.
- Process insurance claims: Provide necessary information for insurance purposes in case of loss or damage.
- Unlock your device from a carrier: Check the lock status and initiate the unlocking process.
Without your iPhone’s serial number, tasks like these become significantly more difficult, or even impossible. Therefore, understanding its significance and knowing how to find it is crucial for any iPhone owner.
Why You Might Need Your iPhone Serial Number
Your iPhone’s serial number is a unique identifier, much like a social security number for your device. It’s crucial for several essential processes.
Here are a few key reasons why you might need to locate your iPhone’s serial number:
- Checking Warranty Status: To verify if your iPhone is still under warranty or covered by AppleCare.
- Repair and Service: Apple or authorized service providers will require the serial number to initiate any repairs.
- Insurance Claims: If your iPhone is lost, stolen, or damaged, your insurance company will need the serial number for the claim process.
- Verifying Authenticity: To confirm that your iPhone is genuine and not a counterfeit product.
- Trade-in or Resale: Potential buyers often request the serial number to check the iPhone’s history and legitimacy.
- Activating Apple Services: Some Apple services or programs may require your device’s serial number for activation or registration.
Having easy access to your iPhone serial number can streamline these processes and save you time and potential frustration.
Finding Your iPhone Serial Number Through Settings
The most straightforward method for locating your iPhone’s serial number is through the device’s settings. This approach is applicable as long as your iPhone is functional and accessible.
Steps to Find Your Serial Number in Settings:
- Unlock your iPhone and navigate to the Home Screen.
- Tap on the Settings app icon.
- Scroll down and select General.
- Tap on About.
- On the About page, scroll down until you see Serial Number. The alphanumeric code displayed next to it is your iPhone’s serial number.
This method provides a quick and easy way to access your iPhone’s serial number without needing to physically inspect the device or access other platforms.
Locating Your iPhone Serial Number on the Device Itself
While the Settings app provides a convenient method for accessing your iPhone’s serial number, it can also be found directly on the device itself in certain instances. This is particularly useful if you cannot power on your iPhone or access the Settings menu.
iPhone Models with Serial Number on the SIM Tray
For certain iPhone models, including the iPhone 6s, iPhone 6s Plus, iPhone SE (1st generation), iPhone 7, iPhone 7 Plus, iPhone 8, iPhone 8 Plus, and iPhone X, the serial number is printed on the SIM tray. To locate it, eject the SIM tray using a SIM eject tool or a straightened paper clip and inspect the tray for the serial number. This method offers a physical backup to accessing the serial number through software.
iPhone Models with Serial Number on the Back of the Device
Older iPhone models sometimes have the serial number etched onto the back of the device. Inspect the back casing for any small print. Note: Apple stopped printing serial numbers on the back of iPhones starting with iPhone 6s due to design changes and security concerns.
Using iTunes/Finder to Find Your iPhone Serial Number
If your iPhone is accessible but you prefer not to navigate through the settings, or you want to find the serial number on a computer, iTunes (on Windows or older macOS versions) or Finder (on newer macOS versions) provides a convenient method.
Steps for iTunes:
- Connect your iPhone to your computer using a USB cable.
- Open iTunes.
- Locate your iPhone icon near the top of the iTunes window.
- Click on the “Summary” tab.
- Your iPhone’s serial number will be displayed next to the “Serial Number” label. You may need to click on “Phone Number” to reveal the serial number.
Steps for Finder (macOS Catalina and later):
- Connect your iPhone to your Mac using a USB cable.
- Open Finder.
- Select your iPhone from the list of devices in the Finder sidebar.
- Click on the “General” tab.
- Your iPhone’s serial number will be displayed. Click on “Phone Number” to reveal the serial number.
Finding the Serial Number on the Original Packaging
If you still possess the original packaging for your iPhone, finding the serial number is remarkably straightforward. Apple typically prints the serial number on a sticker affixed to the exterior of the box.
Here’s how to locate it:
- Examine the Box: Carefully inspect all sides of the original iPhone box.
- Look for a Sticker: The sticker will contain various information, including barcodes, model number, IMEI (if applicable), and most importantly, the serial number.
- Serial Number Location: The serial number is usually clearly labeled as “Serial No.” or “Serial Number” on the sticker.
- Verify Information: Once you’ve located the serial number, double-check it against any other records you might have, such as purchase receipts, to ensure accuracy.
This method is often the quickest and easiest, provided you have retained the original packaging.
How to Find Your iPhone Serial Number if Your Device is Lost or Stolen
Losing your iPhone can be a stressful experience. Fortunately, even if you no longer have physical access to your device, there are methods to potentially retrieve its serial number.
Checking Your Apple ID Account
One of the easiest ways is to check your Apple ID account. Sign in to appleid.apple.com with the Apple ID you used on the missing iPhone. Go to the “Devices” section. You should see a list of all devices associated with your Apple ID. Click on your iPhone; if available, the serial number will be displayed.
Using Other Apple Devices
If you have another Apple device (like an iPad or Mac) that was signed into the same Apple ID, you might be able to find the serial number there. Check the device’s settings under your Apple ID or iCloud account.
Contacting Apple Support
In some cases, Apple Support might be able to assist you in finding your serial number, especially if you can provide them with other identifying information, such as your Apple ID and proof of purchase.
What to Do With Your iPhone Serial Number Once You Find It
Once you have successfully located your iPhone’s serial number, it’s crucial to understand how to utilize this information effectively. The serial number serves as a unique identifier for your device and can be instrumental in various scenarios.
Verification and Record Keeping
First and foremost, verify the authenticity of the serial number against your iPhone’s settings. Note and securely store the serial number in a safe place, such as a password-protected document or a dedicated device management application. This record-keeping will prove invaluable if your iPhone is ever lost or stolen.
Warranty and Support Purposes
The serial number is essential when contacting Apple Support or an authorized service provider for warranty claims, repairs, or technical assistance. They will use the serial number to verify your iPhone’s warranty status and access device-specific information.
Trade-In or Resale
If you plan to trade-in or resell your iPhone, you will likely need to provide the serial number to potential buyers or trade-in services. This allows them to verify the device’s legitimacy and specifications.
Understanding the Format and Information Contained in Your iPhone Serial Number
The iPhone serial number is a unique identifier assigned to each device by Apple. Understanding its format can offer insights into your device’s manufacturing details.
Apple serial numbers have evolved over time. Modern iPhone serial numbers are 12 characters long, while older models used an 11-character format. While Apple no longer publicly documents the exact information encoded, certain characteristics are known.
Here’s a breakdown of what a typical 12-character serial number *might* indicate:
- The first three characters typically represent the manufacturing location.
- Characters 4 and 5 represent the year and week of manufacture.
- The following characters are typically a unique identifier for the device.
Keep in mind that this is a general guide, and Apple can and does change the format of their serial numbers. Using third-party tools or Apple’s warranty check website are more reliable ways to get detailed information about your iPhone based on its serial number.
Troubleshooting Common Issues When Trying to Find Your iPhone Serial Number
Encountering difficulties while trying to locate your iPhone serial number is not uncommon. This section addresses some frequently faced challenges and provides solutions.
Common Problems and Solutions
- Device is Unresponsive: If your iPhone is not powering on, you will not be able to access the serial number through the Settings app. Refer to alternative methods, such as checking the original packaging or using iTunes/Finder on a computer where the iPhone was previously synced.
- Broken Screen: A severely damaged screen can hinder your ability to navigate to the serial number in Settings. If possible, connect your iPhone to a computer and use iTunes/Finder.
- iTunes/Finder Doesn’t Recognize Device: Ensure your computer trusts the connected device. You may need to update iTunes or Finder to the latest version. Restarting both your computer and iPhone can sometimes resolve connectivity issues.
- No Original Packaging: If you no longer possess the original box, and your device is lost or stolen, contacting Apple Support might be your only recourse. You will likely need to provide proof of purchase.
If none of these steps work, contacting Apple Support directly for assistance is highly recommended.
The post Unlock Your Device’s Secrets: A Detailed Guide on How to Find Your iPhone Serial Number Easily appeared first on gadget.apola.co.
]]>The post Staying Safe and Smart: Mastering Public Phone Use for Enhanced Security appeared first on gadget.apola.co.
]]>From identifying potentially compromised phones to employing privacy-enhancing techniques during calls, this comprehensive guide equips you with the knowledge to make smart choices. Learn how to protect your personal information, prevent eavesdropping, and utilize public phones discreetly. Whether you’re a seasoned traveler, a student navigating a new city, or simply someone who wants to be prepared for any situation, the principles outlined here will empower you to use public phones with confidence and prioritize your safety in any environment. Let’s unlock the secrets to secure and smart public phone usage, ensuring your communication remains private and protected.
Why Public Phone Use Requires Extra Caution
Using your phone in public presents unique security risks compared to using it in a private setting. The open nature of public spaces increases the opportunity for eavesdropping, visual surveillance, and unauthorized access to your device and data.
Data interception is a significant concern. Public Wi-Fi networks, often unsecured, can allow malicious actors to intercept data transmitted between your phone and the internet. This includes sensitive information like login credentials, personal details, and financial data.
Moreover, the risk of physical theft is heightened in public. Opportunistic thieves can quickly snatch a phone, leaving the owner vulnerable to identity theft and financial loss. Even simple observation by onlookers can compromise your privacy if you are entering sensitive information.
Therefore, understanding these risks is the first step toward adopting safe practices when using your phone in public environments.
Being Aware of Your Surroundings: A Crucial First Step
Before initiating any activity on your phone in a public setting, it is imperative to assess your immediate environment. This proactive measure is crucial for mitigating potential security risks.
Begin by observing individuals in close proximity. Note their behavior and any indications of suspicious activity. Consider factors such as:
- Proximity: How close are people to you?
- Behavior: Are they paying undue attention to you or your device?
- Environment: Are you in a well-lit, populated area or a secluded location?
Furthermore, be mindful of potential physical threats, such as pickpockets or individuals attempting to snatch your phone. Avoid using your device in crowded or poorly lit areas where such activities are more prevalent. Maintaining situational awareness is your first line of defense against both digital and physical threats.
Securing Your Device: Passwords, Biometrics, and Encryption
Ensuring the security of your device is paramount, particularly when utilizing it in public spaces. This involves implementing robust measures to protect your data and prevent unauthorized access.
Strong Passwords and PINs
Employ strong, unique passwords or PINs. Avoid easily guessable information like birthdays or common words. Regularly update your passwords to maintain optimal security.
Leveraging Biometrics
Utilize biometric authentication methods such as fingerprint scanning or facial recognition. These provide an additional layer of security, making it more difficult for unauthorized individuals to access your device.
Encryption for Data Protection
Enable device encryption. Encryption transforms your data into an unreadable format, ensuring that even if your device is compromised, your information remains protected. Check your device’s settings to verify that encryption is enabled.
Safe Practices for Making Calls in Public
When making calls in public, it is imperative to maintain discretion and avoid revealing sensitive information. Consider the potential for eavesdropping, both physical and electronic.
Lowering your voice can prevent those nearby from overhearing your conversation. If discussing confidential matters, attempt to move to a more secluded area. Be mindful of the volume of your voice, especially in crowded places.
Before answering a call from an unknown number, verify the caller’s identity. Be wary of requests for personal information. Legitimate organizations will typically not ask for sensitive data over the phone.
Avoid discussing financial information, passwords, or other personal details in public. These details should be reserved for secure, private environments.
Terminate the call if you feel uncomfortable or suspect that you are being overheard. It is always better to be safe than sorry.
Protecting Your Data: Avoiding Risky Apps and Downloads
When using your phone in public, the apps you install and the files you download can significantly impact your data security. It is paramount to exercise caution to mitigate potential risks.
Assessing App Security
Before installing any application, carefully review its permissions. Be wary of apps that request excessive access to your personal data, contacts, or location. Only download apps from trusted sources like the official Apple App Store or Google Play Store. Third-party app stores often harbor malicious software.
Risks of Downloading Unverified Files
Avoid downloading files from untrusted sources, especially when using public Wi-Fi. These files can contain malware, viruses, or other harmful software that could compromise your phone’s security and expose your personal information. Always scan downloaded files with a reputable anti-virus app before opening them.
Regularly Review Installed Applications
Periodically review the applications installed on your phone and uninstall any that you no longer use or that seem suspicious. Keep your operating system and apps updated to patch any security vulnerabilities.
Using Public Wi-Fi Networks Securely

Public Wi-Fi networks, while convenient, present significant security risks. These networks are often unsecured, making your data vulnerable to interception.
Here are key steps to ensure secure usage:
- Avoid Sensitive Activities: Refrain from online banking, shopping, or entering passwords on public Wi-Fi.
- Use a Virtual Private Network (VPN): A VPN encrypts your internet traffic, providing a secure tunnel for your data.
- Ensure HTTPS: Look for “HTTPS” in the URL. This indicates a secure connection.
- Disable Automatic Wi-Fi Connection: Prevent your device from automatically connecting to unknown networks.
- Firewall Activation: Enable your device’s firewall for an extra layer of protection.
By adhering to these precautions, you can significantly reduce the risks associated with using public Wi-Fi.
Avoiding Shoulder Surfing: Keeping Your Screen Private
Shoulder surfing, where someone peers over your shoulder to view your screen, is a significant security risk in public settings. It allows onlookers to potentially steal your passwords, PINs, personal messages, and other sensitive information simply by watching what you type or view.
Strategies to Combat Shoulder Surfing
To mitigate this risk, consider the following:
- Be Aware of Your Surroundings: Scan your environment before entering sensitive information. If someone is standing too close, reposition yourself or wait until you’re in a more private location.
- Adjust Screen Brightness: Lowering your screen brightness can make it more difficult for others to see your screen clearly.
- Use a Privacy Screen: A privacy screen filter limits the viewing angle, making it nearly impossible for anyone beside you to see what’s on your screen.
- Be Mindful of Your Typing: Use different fingers or type slowly when entering pin codes
By implementing these preventative measures, you can significantly reduce the risk of falling victim to shoulder surfing and protect your private data in public.
Managing Bluetooth and NFC Connections in Public Spaces
Bluetooth and NFC (Near Field Communication) are convenient technologies, but they can pose security risks in public spaces if not managed carefully. Leaving these connections active when not needed increases your device’s vulnerability to unauthorized access and potential data breaches.
Best Practices:
- Disable Bluetooth and NFC when not in use: Turn off these features in your device settings when you’re not actively using them. This reduces the attack surface available to malicious actors.
- Be cautious when pairing with unknown devices: Avoid pairing with unfamiliar or untrusted devices in public areas. Malicious devices can be disguised to appear legitimate.
- Regularly review paired devices: Periodically check your device’s list of paired Bluetooth devices and remove any that you don’t recognize or no longer use.
- Use strong pairing passcodes: If pairing is necessary, ensure you use a strong and unique passcode.
- Keep your device software updated: Software updates often include security patches that address vulnerabilities related to Bluetooth and NFC.
By taking these precautions, you can significantly reduce the risk of unauthorized access and protect your personal information when using Bluetooth and NFC in public environments.
Utilizing Privacy Screens and Anti-Spyware Apps
In crowded public spaces, visual and digital privacy are paramount. Consider utilizing a privacy screen protector, a thin film applied to your device’s screen that narrows the viewing angle, making it difficult for onlookers to see your screen’s content.
Furthermore, deploy anti-spyware applications. These apps scan your device for malicious software that might be recording your activities, stealing data, or tracking your location. Regularly update your anti-spyware app to ensure it can detect the latest threats.
Here’s a simple breakdown:
- Privacy Screens: Reduce viewing angle, protecting visual data.
- Anti-Spyware Apps: Detect and remove malicious software.
By implementing these tools, you significantly enhance your security posture when using your phone in public.
What to Do If Your Phone is Compromised in Public
If you suspect your phone has been compromised while using it in public, immediate action is crucial to minimize potential damage. Your first step should be to change all critical passwords, including those for your email, banking, and social media accounts. Do this from a secure device, not the compromised phone.
Next, contact your bank and credit card companies to alert them to the potential breach. They can monitor your accounts for suspicious activity and issue new cards if necessary.
Consider reporting the incident to the authorities, especially if you believe your personal information has been stolen. Finally, perform a factory reset on your phone to erase all data. Remember to back up your essential data regularly so you can restore it to a new or secure device.
The post Staying Safe and Smart: Mastering Public Phone Use for Enhanced Security appeared first on gadget.apola.co.
]]>The post Fortress Mode Activated: A Comprehensive Guide to Securing Your Phone with Two-Factor Authentication (2FA) appeared first on gadget.apola.co.
]]>This comprehensive guide delves into the fundamentals of 2FA, explaining how it works and why it is a critical component of modern mobile security. We’ll explore various 2FA methods available, including authenticator apps, SMS codes, and hardware security keys, empowering you to choose the best option for your needs. Whether you’re a seasoned tech enthusiast or new to the world of cybersecurity, “Fortress Mode Activated” will equip you with the tools to significantly reduce the risk of unauthorized access and maintain control over your digital identity.
What is Two-Factor Authentication (2FA) and Why is it Important?
Two-Factor Authentication (2FA) is a security process that requires two different authentication factors to verify a user’s identity. Instead of relying solely on a password, 2FA adds an extra layer of security, significantly reducing the risk of unauthorized access.
The core concept of 2FA rests on the principle of “something you know” (your password) and “something you have” (a code from your phone, a hardware key, etc.). This combination makes it considerably harder for attackers to compromise your account, even if they obtain your password through phishing or data breaches.
Why is 2FA important?
- Enhanced Security: Significantly reduces the risk of unauthorized access to your accounts.
- Protection Against Phishing: Even if you fall victim to a phishing scam, the attacker will still need your second factor, which they are unlikely to have.
- Mitigation of Password Breaches: If your password is compromised in a data breach, 2FA prevents attackers from using it to access your accounts.
- Peace of Mind: Knowing that your accounts are protected by an extra layer of security can provide peace of mind.
In today’s digital landscape, where cyber threats are increasingly sophisticated, implementing 2FA is a crucial step in safeguarding your personal and financial information.
Understanding the Different Types of 2FA Methods: SMS, Authenticator Apps, and Hardware Keys
Two-Factor Authentication (2FA) employs various methods to bolster security. Understanding these options is crucial for selecting the most appropriate method for your needs.
SMS-Based 2FA
SMS-based 2FA sends a verification code to your phone via text message. While convenient, it’s considered the least secure method due to potential interception or SIM swapping attacks.
Authenticator Apps
Authenticator apps (e.g., Google Authenticator, Authy) generate time-based, one-time passwords (TOTP) on your device. These apps are generally more secure than SMS, as they don’t rely on cellular networks. They require initial setup involving scanning a QR code.
Hardware Keys
Hardware keys (e.g., YubiKey, Google Titan Security Key) are physical devices that provide the strongest form of 2FA. They utilize cryptographic authentication, making them highly resistant to phishing attacks. They typically connect via USB or NFC.
How to Enable 2FA on Your Google Account for Enhanced Security
Enabling Two-Factor Authentication (2FA) on your Google Account significantly strengthens its security. This process adds an extra layer of protection beyond your password, making it considerably harder for unauthorized individuals to gain access.
Steps to Enable 2FA on Your Google Account:
- Navigate to your Google Account settings. This can be accessed by clicking on your profile picture in the upper right corner of any Google service (e.g., Gmail, YouTube) and selecting “Manage your Google Account.”
- In the left navigation panel, select “Security.”
- Under the “Signing in to Google” section, find “2-Step Verification” and click on it.
- Click “Get Started” and follow the on-screen instructions.
- You will be prompted to enter your password.
- Choose your preferred 2FA method (e.g., Google Prompt, Authenticator App, Security Key).
- Follow the instructions to set up your chosen method. This may involve downloading the Google Authenticator app or registering a security key.
- Once set up, Google will provide backup codes. Store these codes in a safe place as they are essential for regaining access to your account if you lose access to your primary 2FA method.
After completing these steps, 2FA will be enabled on your Google Account. You will now be required to use a second factor of authentication in addition to your password when signing in from a new device or location.
Securing Social Media Accounts with 2FA: Facebook, Instagram, and Twitter
Social media platforms are prime targets for malicious actors. Enabling two-factor authentication (2FA) on these accounts is crucial for bolstering your online security. Here’s how to secure your Facebook, Instagram, and Twitter profiles:
Navigate to Settings & Privacy > Settings > Security and Login > Use two-factor authentication. Choose your preferred method (authenticator app or SMS) and follow the on-screen instructions to complete the setup. Facebook offers both options.
Go to Settings > Security > Two-Factor Authentication. Turn on either Text Message or Authentication App. Follow the prompts to link your phone number or preferred authenticator app. Instagram highly recommends using an authenticator app for superior security.
Twitter (X)
Access Settings and Support > Settings and privacy > Security and account access > Security > Two-factor authentication. Select your preferred method (text message, authentication app, or security key) and follow the instructions provided. X (formerly Twitter) provides flexible options for 2FA.
Protecting Email Accounts with 2FA: Gmail, Outlook, and Yahoo Mail

Securing your email accounts with Two-Factor Authentication (2FA) is a crucial step in protecting your personal information from unauthorized access. Given the sensitive data often stored in email, enabling 2FA adds a significant layer of security.
Gmail
To enable 2FA on Gmail, navigate to your Google Account security settings. Locate the “2-Step Verification” option and follow the prompts to set up 2FA using your preferred method, such as Google Authenticator or SMS codes.
Outlook
For Outlook, access your Microsoft Account security dashboard. Find the “Two-step verification” settings and enable the feature. You can then choose to receive codes via the Microsoft Authenticator app or SMS.
Yahoo Mail
To activate 2FA on Yahoo Mail, go to your Account security settings. Look for the “Two-step verification” option and follow the instructions to set it up. Yahoo offers various options, including using the Yahoo Account Key app or receiving verification codes via SMS.
By implementing 2FA on your email accounts, you significantly reduce the risk of unauthorized access, even if your password is compromised.
Enabling 2FA on Banking and Financial Apps for Added Protection
Securing your banking and financial applications with Two-Factor Authentication (2FA) is paramount in protecting your sensitive financial data from unauthorized access. Given the high value target these applications represent, enabling 2FA adds a significant layer of security.
Why Enable 2FA on Financial Apps?
Financial applications often contain highly sensitive information, including bank account details, credit card numbers, and investment portfolios. 2FA drastically reduces the risk of account compromise even if your password becomes known to a malicious actor.
Steps to Enable 2FA:
- Access App Settings: Navigate to the settings or security section within your banking or financial app.
- Locate 2FA Option: Look for options such as “Two-Factor Authentication,” “Multi-Factor Authentication,” or “Security Settings.”
- Choose 2FA Method: Select your preferred 2FA method, typically an authenticator app or SMS verification.
- Follow On-Screen Instructions: Complete the setup process by scanning the QR code or entering the provided key into your authenticator app.
- Save Backup Codes: Store the backup codes in a secure location, accessible only to you. These are vital for account recovery if you lose access to your primary 2FA method.
By implementing 2FA on your banking and financial apps, you significantly strengthen your overall security posture and protect your valuable assets.
Managing and Backing Up Your 2FA Codes for Recovery Purposes
Two-Factor Authentication (2FA) significantly enhances security, but it’s crucial to manage and back up your 2FA codes to avoid being locked out of your accounts. Losing access to your 2FA method can be a frustrating experience, therefore proactive measures are essential.
Importance of Backup
Backing up your 2FA codes or recovery methods provides a safety net if you lose your device, change phone numbers, or encounter issues with your authenticator app. Without a backup, account recovery can be lengthy and potentially unsuccessful.
Methods for Backing Up 2FA Codes
Several methods exist for safeguarding your 2FA access:
- Recovery Codes: Most services provide recovery codes upon enabling 2FA. Store these codes in a secure, offline location such as a password manager or a physical document kept in a safe place.
- Authenticator App Backup: Some authenticator apps offer cloud backup features. Ensure these backups are enabled and secured with a strong password.
- Multiple Devices: Configure 2FA on multiple devices if the service allows. This provides redundancy if one device is lost or damaged.
Regular Verification
Periodically verify that your backup methods are functional. Test your recovery codes to ensure they work as expected, and confirm that your authenticator app backups are up-to-date. This proactive approach can prevent significant issues in the future.
Troubleshooting Common Issues with 2FA: Lost Devices and Code Generation
Encountering difficulties with Two-Factor Authentication (2FA) can be frustrating. This section addresses common issues and provides solutions.
Lost Devices
Losing a device with your 2FA codes is a frequent problem. Ensure you have a recovery plan in place. This usually involves:
- Recovery Codes: Many services provide backup codes to use when you can’t access your device. Store these securely.
- Trusted Devices: Some platforms allow you to designate trusted devices that don’t require 2FA every time.
- Account Recovery: Contact the service provider’s support team for assistance with account recovery.
Code Generation Problems
Issues with code generation can stem from:
- Incorrect Time: Authenticator apps rely on accurate time. Ensure your device’s time is synchronized.
- App Issues: Try clearing the app’s cache or reinstalling it.
- Service Issues: Occasionally, the service provider may have temporary issues with 2FA.
It’s crucial to address these problems promptly to maintain access to your accounts. Always prioritize having backup methods and understanding the recovery processes.
Best Practices for Maintaining a Strong and Secure 2FA Setup
Once you’ve implemented two-factor authentication (2FA), it’s crucial to maintain a strong and secure setup. This ensures ongoing protection against unauthorized access.
Regularly Review and Update Your 2FA Settings
Periodically review your 2FA settings across all platforms. Ensure that your recovery options are up-to-date, including your recovery email and phone number. Update your 2FA methods when necessary to incorporate stronger options as they become available.
Secure Your Recovery Codes
When enabling 2FA, you’re often provided with recovery codes. These codes are essential if you lose access to your primary 2FA method. Store them securely in a password manager or a safe physical location, separate from your phone.
Be Wary of Phishing Attempts
Phishing attempts can bypass 2FA if you’re not vigilant. Always verify the legitimacy of any website or email requesting your 2FA code. Never enter your code into a suspicious website or share it with an untrusted source.
Monitor Account Activity
Regularly check your account activity for any unusual or unauthorized logins. This helps you identify potential security breaches promptly, even with 2FA enabled.
Exploring Advanced Security Options Beyond 2FA: Biometric Authentication and Password Managers
While two-factor authentication (2FA) significantly bolsters your online security, exploring advanced security measures can further fortify your defenses. These options, such as biometric authentication and password managers, offer additional layers of protection against unauthorized access.
Biometric Authentication
Biometric authentication utilizes unique biological traits for identification, such as fingerprints, facial recognition, or voice analysis. Integrating biometrics can provide a seamless and secure login experience, minimizing reliance on passwords alone. Many devices and applications now offer built-in biometric authentication options.
Password Managers
Password managers securely store and generate complex, unique passwords for all your accounts. They typically offer features such as auto-filling login credentials and identifying weak or reused passwords. Using a reputable password manager reduces the risk of password-related breaches and simplifies password management across multiple platforms.
The post Fortress Mode Activated: A Comprehensive Guide to Securing Your Phone with Two-Factor Authentication (2FA) appeared first on gadget.apola.co.
]]>The post Shield Up! Robust Strategies to Protect Your Phone from Viruses and Malware Threats appeared first on gadget.apola.co.
]]>This guide will provide a comprehensive overview of the common viruses and malware that target smartphones, including Android and iOS devices. We will explore practical steps you can take to enhance your phone’s security, from installing reputable antivirus software and enabling security features to practicing safe browsing habits and recognizing phishing attempts. Learn how to create a robust defense against these digital threats and enjoy a safer, more secure mobile experience. This isn’t just about protecting your phone; it’s about safeguarding your digital life.
Understanding the Threat Landscape: Common Types of Mobile Viruses and Malware
Mobile devices, like smartphones and tablets, are increasingly targeted by malicious software. Understanding the common types of mobile viruses and malware is crucial for effective protection.
Common Malware Types
- Adware: Displays unwanted advertisements, often aggressively.
- Spyware: Secretly monitors user activity and collects sensitive information.
- Ransomware: Encrypts a device’s data and demands a ransom for its release.
- Trojans: Disguise themselves as legitimate apps to gain access to a device.
- Worms: Self-replicating malware that spreads to other devices.
- Banking Trojans: Steal banking credentials and financial information.
Key Distribution Methods
Malware often spreads through:
- Malicious apps downloaded from unofficial app stores.
- Phishing emails and SMS messages containing malicious links.
- Compromised websites.
The Importance of Installing a Reputable Antivirus App on Your Phone
In the contemporary digital environment, mobile devices are increasingly susceptible to malicious software. Installing a reputable antivirus application on your phone is crucial for maintaining the security and integrity of your data. These apps provide a vital layer of defense against a wide range of threats, including viruses, malware, spyware, and ransomware.
Antivirus applications function by scanning files and applications for known malware signatures, identifying suspicious behavior, and proactively blocking potential threats before they can compromise your device. They also offer features such as real-time protection, which continuously monitors your phone for malicious activity, and scheduled scans, which automatically check your device for threats on a regular basis.
Selecting a reputable antivirus app is paramount. Opt for well-established brands with a proven track record of effectively detecting and removing malware. Read reviews, compare features, and ensure the app is compatible with your phone’s operating system. Free antivirus apps may offer basic protection, but often lack advanced features and may contain advertisements. Consider investing in a paid subscription for more comprehensive security.
How to Scan Your Phone for Viruses and Malware Using an Antivirus App
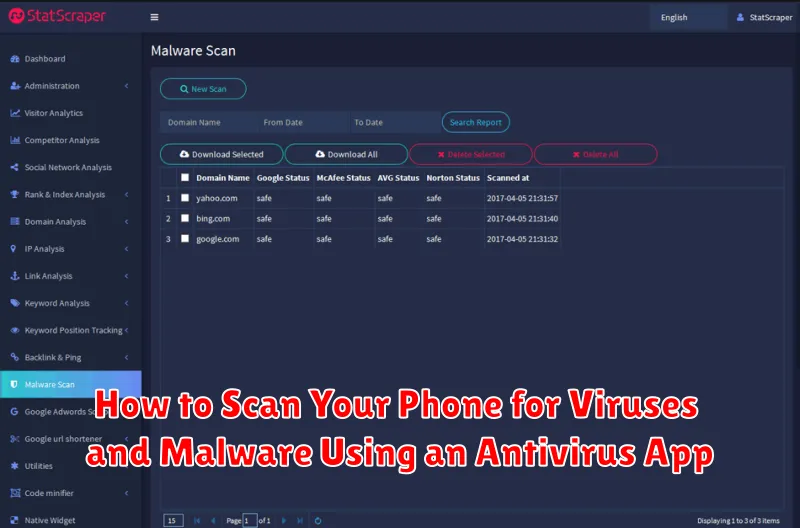
Once a reputable antivirus application is installed on your phone, performing a scan is a crucial step in maintaining its security. Here’s a general overview of how to initiate and interpret a scan:
- Open the Antivirus App: Locate the antivirus application on your phone and open it.
- Initiate a Scan: Look for an option labeled “Scan,” “Smart Scan,” or something similar. Tap this button to begin the scanning process.
- Select Scan Type (If Available): Some apps offer different scan types, such as “Quick Scan” for a fast check or “Full Scan” for a more comprehensive analysis. A full scan is recommended for the first time.
- Allow Permissions: The app may request permissions to access files and system data for a thorough scan. Grant these permissions to ensure complete coverage.
- Review Scan Results: After the scan completes, the app will display a list of detected threats.
- Take Action: Follow the app’s recommendations to quarantine, delete, or resolve any identified malware or suspicious files.
It is advisable to perform regular scans, at least once a week, or more frequently if you suspect a potential threat.
Enabling Google Play Protect for Real-time Threat Detection
Google Play Protect is a built-in security feature on Android devices that provides real-time threat detection. It continuously scans apps from the Google Play Store and other sources for malware and suspicious behavior. Enabling Play Protect is a crucial step in maintaining your phone’s security.
How to Enable Google Play Protect:
- Open the Google Play Store app.
- Tap on your profile icon in the top right corner.
- Select Play Protect.
- Ensure that the “Scan apps with Play Protect” option is turned on.
Play Protect also sends warnings if it detects potentially harmful apps, giving you the opportunity to uninstall them before they can cause damage. It’s important to heed these warnings and take appropriate action to protect your device and data.
Practicing Safe Browsing Habits: Avoiding Suspicious Websites and Links
Safe browsing habits are crucial for protecting your phone from viruses and malware. By exercising caution online, you can significantly reduce the risk of infection.
Be Wary of Suspicious Websites
Avoid websites that appear untrustworthy. Red flags include poor grammar, excessive advertisements, and requests for personal information that seem out of place. Always check the website’s URL for misspellings or unusual domain extensions.
Exercise Caution with Links
Be extremely careful before clicking on any link, especially those received in unsolicited emails, text messages, or social media posts. Verify the sender’s authenticity and hover over the link to preview its destination before clicking. Shortened URLs can mask malicious destinations, so proceed with extra caution. It’s better to manually type the address of a known website than to click on a potentially dangerous link.
Look for Security Indicators
Ensure the website uses HTTPS (Hypertext Transfer Protocol Secure) by checking for a padlock icon in the address bar. This indicates that the connection is encrypted and your data is transmitted securely.
Being Cautious with App Downloads: Verifying App Permissions and Authenticity
Downloading applications (apps) is a common activity on smartphones, but it also presents a significant security risk. It is crucial to exercise caution and adopt practices to ensure the apps you install are safe and legitimate.
Verifying App Permissions
Before installing any app, carefully review the permissions it requests. Question any permissions that seem excessive or unrelated to the app’s functionality. For example, a simple calculator app shouldn’t need access to your contacts or location.
Authenticity Checks
Prioritize downloading apps from official app stores like Google Play Store or Apple App Store. These stores have security measures in place, although malware can still occasionally slip through. Before downloading, also check the app developer’s name and reviews, to ascertain whether the application is authentic. A significant number of negative or suspicious reviews should serve as a warning sign.
Utilize Third-Party Tools
Consider using tools that scan downloaded APK files for malware before installation, providing an additional layer of security. These tools can help identify potential threats that may be missed by app store security measures.
Regularly Updating Your Phone’s Operating System and Apps for Security Patches
Regularly updating your phone’s operating system (OS) and applications is crucial for maintaining a secure mobile environment. These updates often include critical security patches that address known vulnerabilities exploited by viruses and malware.
Operating System Updates:
OS updates provided by manufacturers like Apple (iOS) and Google (Android) contain fixes for security flaws discovered in the core system software. Installing these updates promptly minimizes the risk of exploitation.
App Updates:
Similarly, app developers release updates to address bugs and security vulnerabilities within their applications. Keeping your apps updated ensures that you are running the latest versions with the most recent security enhancements.
How to Update:
Enable automatic updates in your phone’s settings for both the OS and individual apps. Alternatively, manually check for updates regularly through the Google Play Store (Android) or App Store (iOS).
Benefits:
- Enhanced Security: Patches address known vulnerabilities.
- Improved Performance: Updates often include performance optimizations.
- New Features: Updates may introduce new features and functionalities.
Recognizing Phishing Attempts: Identifying and Avoiding Malicious Emails and Messages
Phishing is a deceptive tactic cybercriminals use to trick you into revealing sensitive information, such as passwords, credit card details, or personal data. These attempts often come in the form of emails, text messages, or even phone calls that appear to be legitimate.
Identifying Phishing Attempts:
- Generic Greetings: Be wary of emails that begin with “Dear Customer” instead of your name.
- Suspicious Links: Hover over links before clicking to see the actual URL. Does it match the sender’s claimed website?
- Urgent Requests: Phishing attempts often create a sense of urgency to pressure you into acting quickly without thinking.
- Poor Grammar and Spelling: Look for typos, grammatical errors, and unprofessional language.
- Requests for Personal Information: Legitimate organizations rarely ask for sensitive information via email or text.
Avoiding Phishing Attacks:
- Never click on suspicious links or open attachments from unknown senders.
- Verify the sender’s identity by contacting the organization directly through a known phone number or website.
- Be cautious of unsolicited emails or messages, even if they appear to be from a trusted source.
- Report phishing attempts to the relevant authorities or organizations.
Securing Your Wi-Fi Connection: Avoiding Unsecured Public Networks
Unsecured public Wi-Fi networks pose a significant security risk to your mobile device. These networks often lack encryption, making your data vulnerable to interception by malicious actors.
When connected to an unsecured network, sensitive information such as passwords, financial details, and personal data can be easily compromised.
To mitigate this risk, adhere to the following practices:
- Avoid connecting to unsecured public Wi-Fi networks whenever possible.
- If you must use public Wi-Fi, use a Virtual Private Network (VPN) to encrypt your internet traffic.
- Ensure that any websites you visit use HTTPS (indicated by a padlock icon in the address bar), which encrypts data transmitted between your device and the website.
- Refrain from conducting sensitive transactions, such as online banking or shopping, on unsecured public Wi-Fi networks.
- Consider using your mobile data connection instead of public Wi-Fi for added security.
Backing Up Your Data Regularly to Prevent Data Loss from Malware Attacks
Regularly backing up your phone’s data is crucial in mitigating the impact of malware attacks. Malware can lead to data corruption, deletion, or encryption, making your information inaccessible. By maintaining current backups, you can restore your phone to a clean state, minimizing data loss.
Consider these backup methods:
- Cloud Storage: Utilize services like Google Drive, iCloud, or Dropbox for automatic backups.
- Local Backup: Transfer files to a computer or external hard drive.
- Manufacturer’s Backup Solutions: Explore backup options provided by your phone’s manufacturer.
Schedule backups regularly, ideally weekly or even daily for critical data. Ensure your backup contains essential data like contacts, photos, videos, documents, and app data. Regularly test your backups to ensure they are functioning correctly.
The post Shield Up! Robust Strategies to Protect Your Phone from Viruses and Malware Threats appeared first on gadget.apola.co.
]]>The post Spotting the Fakes: A Guide on How to Identify Fake Apps on the Play Store appeared first on gadget.apola.co.
]]>This guide, “Spotting the Fakes: A Guide on How to Identify Fake Apps on the Play Store,” is designed to equip you with the knowledge and skills necessary to navigate the Play Store safely and avoid becoming a victim of fake app scams. We will delve into the key indicators of a fraudulent app, from examining developer profiles and user reviews to scrutinizing app permissions and design elements. By understanding these red flags, you can significantly reduce your risk of downloading and installing malicious software on your device.
Why are Fake Apps a Problem?
Fake apps present a significant threat to user security and data privacy. These deceptive applications often mimic legitimate ones to trick users into downloading them.
One major issue is malware distribution. Fake apps frequently contain viruses, trojans, and other malicious software that can compromise your device and steal sensitive information such as passwords, credit card details, and personal data.
Furthermore, they can lead to financial losses through fraudulent charges, subscription scams, or by redirecting users to phishing websites designed to steal credentials. Another concern is the potential for data breaches, as fake apps may collect and transmit your data to unauthorized third parties.
Finally, the presence of fake apps erodes trust in the app ecosystem, making users more hesitant to download new applications, even those from legitimate developers.
Checking Developer Information: A Key Indicator
A crucial step in identifying fake apps is to examine the developer information. Legitimate apps are typically published by reputable developers with a history of creating reliable software. When viewing an app on the Play Store, carefully inspect the developer’s name. Does it match the official company or brand?
Here’s what to look for:
- Developer Name: Is it spelled correctly and does it align with the official company’s name? Typos are a major red flag.
- Developer Website: Does the developer have a legitimate website? A link to the website should be available on the app’s Play Store page. Verify that the website is professional and provides contact information.
- Developer Address: Legitimate developers often provide a physical address. The absence of an address, or a vague one, could indicate a fake app.
- Other Apps: Check what other apps the developer has published. Do they seem legitimate and related, or are they a random assortment of unrelated apps?
Be suspicious of developers with generic names, missing contact information, or a lack of a professional online presence. These are strong indicators of a potentially fake app.
Examining App Permissions: What Are They Accessing?
One of the most crucial steps in identifying fake or malicious apps is carefully examining the permissions they request. Legitimate apps will only ask for permissions necessary for their core functionality. Fake apps, however, may request excessive or irrelevant permissions to gain access to your personal data.
Consider these points:
- Why does this app need this permission? If a flashlight app requests access to your contacts, it’s a red flag.
- Is the scope of the permissions too broad? An app might need location access, but does it really need precise location when a general area would suffice?
Be particularly wary of apps requesting permissions related to:
- Contacts
- SMS messages
- Call logs
- Camera
- Microphone
- Location (especially continuous background access)
If an app’s requested permissions seem suspicious or excessive, it’s best to avoid downloading it. Always prioritize your privacy and security by carefully scrutinizing what an app wants to access on your device.
Reading User Reviews: What Are Others Saying?
User reviews offer valuable insights into the legitimacy and functionality of an app. Before downloading, take the time to carefully read through a variety of reviews, paying attention to both positive and negative feedback.
Look for recurring themes or complaints. Are multiple users reporting similar issues, such as crashes, unexpected behavior, or intrusive advertising? A high volume of negative reviews, especially those mentioning potential security risks or misleading functionality, should raise a red flag.
Be aware that fake apps may also feature fake reviews. Watch out for reviews that sound generic, overly enthusiastic, or use suspiciously similar language. Genuine reviews tend to be more specific and provide details about the user’s experience.
Consider the overall rating of the app. While a few negative reviews are normal, a consistently low rating (below 3 stars) is a strong indication that the app may not be trustworthy.
Analyzing Download Numbers: Does it Seem Legitimate?
Download numbers can provide a significant clue about the legitimacy of an app. While not a foolproof method, a very low number of downloads for an app that claims to be popular should raise a red flag. Established and legitimate apps usually boast download numbers in the thousands, if not millions.
Consider the app’s purported function and age. A newly released app, even if legitimate, might have fewer downloads initially. However, a fake app mimicking a well-known, established app and displaying only a handful of downloads is highly suspicious.
Furthermore, be wary of suspiciously inflated download numbers. While harder to detect, unrealistically high download numbers in a short period, particularly coupled with poor reviews, may indicate the use of bots or other fraudulent methods to artificially inflate popularity.
Comparing App Icons and Names with Official Versions
One of the most straightforward methods to identify fake apps involves a close comparison of the app’s icon and name with the official version. Fake apps often attempt to mimic legitimate ones, but subtle differences can be revealing.
Icon discrepancies might include variations in color, resolution, or design elements. Pay close attention to the sharpness and overall quality of the icon; fake apps often have poorly rendered or pixelated icons.
Similarly, scrutinize the app’s name. Fake apps may use slight misspellings, added characters, or variations in capitalization to deceive users. Compare the name directly to the official app listing on the Google Play Store to ensure accuracy. For example, “Faceboook” instead of “Facebook.”
If possible, visit the official website of the app developer to confirm the correct icon and naming convention used for their application.
Being Wary of Suspicious Updates and Requests
Staying vigilant about app updates and permission requests is crucial in identifying potentially fake or malicious applications. Fake apps often mimic legitimate software but may contain malware or seek to steal your data.
Examine update details carefully. Be suspicious of updates that:
- Arrive shortly after you install the app (could indicate rushed or sloppy development).
- Request significantly more permissions than the app initially required.
- Lack clear release notes or descriptions of the changes made.
Be cautious of unusual permission requests. If an app, especially one you’ve used for a while, suddenly asks for access to your contacts, location, or other sensitive data that seems irrelevant to its function, proceed with extreme caution. Deny the permission if you’re unsure.
Verify the app’s legitimacy before installing any updates or granting new permissions. Check the developer’s information and user reviews as described in other sections of this guide.
Using Antivirus Apps for Extra Protection
Employing antivirus applications is a proactive measure in safeguarding your device against malicious fake apps. These apps scan installed applications and files for known malware signatures and suspicious behavior.
How Antivirus Apps Help:
- Real-time Scanning: Continuously monitors apps and files as they are accessed.
- Malware Detection: Identifies and removes known malware threats.
- Suspicious Activity Alerts: Notifies you of apps exhibiting unusual behavior, such as excessive data usage or unauthorized access to device features.
While not foolproof, integrating a reputable antivirus solution provides an additional layer of security. Ensure the antivirus app itself is legitimate by downloading it from the official Google Play Store and verifying the developer’s credentials.
Reporting Fake Apps to the Google Play Store
Once you have identified a potentially fake app, it is crucial to report it to the Google Play Store. Reporting helps protect other users from downloading and using malicious or misleading applications.
Steps to Report an App:
- Open the Google Play Store app.
- Navigate to the app listing you want to report.
- Tap the three vertical dots (menu) in the top-right corner of the app’s page.
- Select “Flag as inappropriate.”
- Choose the reason that best describes why you are reporting the app (e.g., “Copycat app,” “Spam,” “Inappropriate content”).
- Submit your report.
By taking these steps, you contribute to a safer app ecosystem and help Google identify and remove fraudulent applications from the Play Store.
Staying Informed About Common Scam Tactics

Staying informed about common scam tactics is crucial in protecting yourself from fake apps. Cybercriminals constantly evolve their methods, making it imperative to stay updated on the latest threats.
Phishing Attempts: Be wary of apps that request personal information upfront, especially if it seems unusual or unnecessary. Legitimate apps typically request such information within a secure environment, after establishing trust.
Subscription Traps: Many fake apps lure users with free trials, then automatically enroll them in expensive subscriptions. Read the fine print carefully and be cautious of overly aggressive promotional tactics.
Adware & Malware Disguises: Some fake apps are designed to inundate your device with unwanted ads or even install malware. Regularly scan your device with a reputable antivirus program.
Fake Updates: Be skeptical of unusual update requests outside the Play Store’s official channels. Scammers may use fake updates to install malicious software.
Checking App Description

The app description on the Google Play Store is a critical source of information. Scrutinize it carefully for red flags indicative of a fraudulent application. Authentic apps usually feature well-written, grammatically correct descriptions that accurately reflect the app’s functionality and purpose.
Look for the following:
- Poor Grammar and Spelling: Numerous errors suggest a lack of professionalism and potential fraud.
- Vague or Generic Descriptions: Authentic apps clearly state their features and benefits.
- Unrealistic Claims: Be wary of descriptions promising extraordinary results or features that seem too good to be true.
- Inconsistencies: Ensure the description aligns with the app’s title, developer, and advertised functionality.
- Excessive Keywords: Overuse of keywords to manipulate search rankings can be a sign of a low-quality or fake app.
Compare the description with that of the official app (if you know it). Discrepancies are a major cause for concern. A legitimate developer takes time to create a detailed and accurate description of the application.
The post Spotting the Fakes: A Guide on How to Identify Fake Apps on the Play Store appeared first on gadget.apola.co.
]]>The post Secure Your Mobile Life: A Comprehensive Guide on How to Connect to VPN on Your Phone appeared first on gadget.apola.co.
]]>Whether you’re an Android or iOS user, understanding how to configure a VPN on your smartphone is crucial for safeguarding your digital footprint. This guide provides detailed instructions, covering everything from choosing the right VPN provider to setting up the connection and troubleshooting common issues. By following these guidelines, you can confidently protect your data from prying eyes, browse the internet with greater anonymity, and access geographically restricted content, ultimately empowering you to take control of your mobile security. Let’s dive in and discover how to secure your mobile life with the power of VPN technology.
What is a VPN and Why Use It on Your Phone?
A VPN, or Virtual Private Network, is a service that creates a secure, encrypted connection over a less secure network. It essentially masks your IP address, providing online privacy and anonymity.
There are several compelling reasons to use a VPN on your phone:
- Enhanced Security on Public Wi-Fi: Public Wi-Fi networks are often unsecured, making your data vulnerable to interception. A VPN encrypts your traffic, protecting your sensitive information.
- Bypassing Geo-Restrictions: Access content that may be blocked in your region due to geographical restrictions.
- Increased Privacy: Prevent your internet service provider (ISP) and other entities from tracking your online activity.
- Secure Data Transfer: Protect sensitive information when accessing banking apps or performing other transactions on your phone.
Understanding VPN Protocols: OpenVPN, IKEv2, and More
VPN protocols are the backbone of secure and private internet connections. They dictate how data is encrypted and transmitted between your device and the VPN server. Understanding these protocols is crucial for selecting a VPN that meets your specific needs.
Key VPN Protocols:
- OpenVPN: Widely regarded as one of the most secure and versatile protocols, OpenVPN is open-source and highly customizable. It supports various encryption algorithms and is compatible with most operating systems.
- IKEv2/IPsec: Known for its speed and stability, IKEv2 (Internet Key Exchange version 2) is often paired with IPsec (Internet Protocol Security). It’s particularly effective at maintaining a connection when switching between networks, making it ideal for mobile devices.
- WireGuard: A relatively new protocol, WireGuard is gaining popularity due to its simplicity and high performance. It uses state-of-the-art cryptography and offers excellent speeds.
- L2TP/IPsec: While still used, L2TP (Layer 2 Tunneling Protocol) itself doesn’t provide encryption. It’s typically combined with IPsec for security. However, it can be slower and potentially less secure than OpenVPN or IKEv2.
- PPTP: An older protocol, PPTP (Point-to-Point Tunneling Protocol) is generally considered insecure and should be avoided.
The choice of VPN protocol significantly impacts your security, speed, and overall experience. Consider your priorities when selecting a VPN protocol for your mobile device.
How to Manually Configure a VPN Connection on Android
Configuring a VPN connection manually on an Android device grants you greater control over your privacy and security. This method is particularly useful if you have specific VPN server details or wish to avoid using a third-party application.
Here’s a concise guide to setting up a manual VPN connection on your Android:
- Navigate to your device’s Settings menu.
- Select Network & Internet or a similarly named option (the exact wording may vary depending on your Android version).
- Tap on VPN. If you don’t see VPN directly, it might be under “Advanced” or “More connections.”
- Tap the “+” icon or “Add VPN network.”
- Enter the necessary information provided by your VPN service, including:
- Name (a descriptive name for the connection)
- Type (the VPN protocol, e.g., PPTP, L2TP/IPSec PSK, IKEv2/IPSec MSCHAPv2)
- Server address
- IPSec pre-shared key (if required by the protocol)
- Username
- Password
- Tap Save.
- To connect, tap the VPN you just created and enter your credentials if prompted.
Be sure to verify the configuration details with your VPN provider to ensure a successful connection.
How to Connect to a VPN on iOS Devices
Connecting to a VPN on your iOS device (iPhone or iPad) is straightforward. You can either use a dedicated VPN app or manually configure the connection.
Connecting via VPN App
This is the simplest method. Download and install your chosen VPN app from the App Store. Once installed, open the app and follow the on-screen instructions. You will likely need to grant the app permission to configure VPN settings on your device. After that, you can usually connect to a VPN server with a single tap.
Manually Configuring a VPN Connection
To manually configure a VPN:
- Go to Settings > General > VPN.
- Tap Add VPN Configuration…
- Enter the VPN settings provided by your VPN service, including:
- Type (e.g., IKEv2, IPSec, L2TP)
- Description (a name for the connection)
- Server address
- Account username
- Password
- Remote ID (if required)
- Tap Done.
- Toggle the switch next to the connection name to connect to the VPN.
Best VPN Apps for Mobile: Features, Security, and Speed
Choosing the right VPN app for your mobile device involves evaluating several crucial factors. Features, security, and speed are paramount. Consider the following aspects when selecting a VPN app:
- Encryption Strength: Look for AES-256 encryption or equivalent for robust data protection.
- No-Logs Policy: Ensure the provider has a strict no-logs policy to prevent tracking of your online activity.
- Server Locations: A wide network of servers across various countries ensures better speed and access to geo-restricted content.
- Kill Switch: A kill switch automatically disconnects your internet if the VPN connection drops, preventing data leaks.
- User Interface: The app should be intuitive and easy to navigate on a mobile screen.
- Speed: Test the speed of different servers to ensure a fast and reliable connection.
Popular VPN apps often include features like split tunneling (allowing certain apps to bypass the VPN), dedicated IP addresses, and multi-hop connections for enhanced security. Compare these features to determine which app best suits your specific needs and prioritize your requirements based on feature, security, and speed.
Troubleshooting Common VPN Connection Issues on Phones
Encountering issues while connecting to a VPN on your phone can be frustrating. This section provides solutions to common problems.
Connectivity Problems
If your VPN fails to connect, first verify your internet connection. Ensure your Wi-Fi or mobile data is active and functioning correctly. Next, check your VPN app’s configuration settings, including server address and protocol.
Slow VPN Speed
Slow speeds can be caused by server distance or congestion. Try connecting to a server closer to your location. Also, experiment with different VPN protocols, as some are faster than others. Closing other bandwidth-intensive apps can also help.
VPN Disconnecting Frequently
Frequent disconnections might indicate an unstable internet connection. If using Wi-Fi, move closer to the router. Check your phone’s battery-saving settings, as these can sometimes interfere with VPN connections. Reinstalling the VPN app is also an option.
Authentication Errors
Authentication errors typically arise from incorrect username or password entries. Double-check your login credentials within the VPN app. If you’ve forgotten your password, use the password recovery option provided by your VPN service.
Using a VPN on Public Wi-Fi Networks: Staying Safe
Public Wi-Fi networks are often unsecured, making them a prime target for cybercriminals. Connecting to these networks without adequate protection can expose your sensitive data to various risks, including data interception, man-in-the-middle attacks, and malware distribution.
A VPN provides a crucial layer of security when using public Wi-Fi. It encrypts your internet traffic, preventing eavesdroppers from accessing your passwords, financial information, and browsing history. This encryption creates a secure tunnel for your data, shielding it from potential threats.
Always activate your VPN before connecting to a public Wi-Fi network. Verify that the VPN connection is stable and active throughout your browsing session. Even seemingly harmless activities like checking emails or social media can be compromised on unsecured networks. A VPN is your essential shield in such environments, ensuring your online safety and data privacy.
The Legality of Using VPNs: Understanding the Rules
The legality of using a VPN (Virtual Private Network) varies significantly from country to country. In many nations, including the United States, Canada, the United Kingdom, and most of the European Union, using a VPN is perfectly legal. Individuals can use VPNs to protect their privacy, access region-locked content, and secure their internet connection.
However, some countries have restrictions or outright bans on VPN usage. China, Russia, North Korea, and Belarus are known for their strict internet censorship and control, making VPN use either illegal or heavily restricted. In these regions, the government often monitors and blocks VPN services in an attempt to control the flow of information.
It’s crucial to understand the specific laws and regulations regarding VPNs in your current location or any country you plan to visit. While using a VPN might be legal, using it for illegal activities remains illegal. Using a VPN to engage in cybercrime, hacking, or accessing illegal content will still have legal consequences.
Free vs. Paid VPN Services: What You Need to Know
When choosing a VPN for your mobile device, one of the initial decisions you’ll face is whether to opt for a free or a paid service. Both offer distinct advantages and disadvantages that should be carefully considered.
Free VPNs often come with limitations, such as data caps, slower connection speeds, and a restricted selection of servers. Critically, some free VPNs may monetize your data by logging your browsing activity or displaying intrusive advertisements. Security may also be compromised as free services may lack robust encryption protocols.
Paid VPNs typically provide unlimited data, faster speeds, and a broader range of servers globally. They generally offer stronger security features, including advanced encryption and a strict no-logs policy, ensuring your privacy. Furthermore, paid services often include dedicated customer support, improving the user experience.
Ultimately, the best choice depends on your specific needs and priorities. If you require basic privacy and are a light user, a free VPN might suffice. However, if you value security, speed, and unlimited data, a paid VPN is generally the more reliable and secure option.
Optimizing Your VPN Connection for Better Performance
Experiencing slow speeds or inconsistent connections with your VPN? Several factors can influence VPN performance on your phone. Optimizing these can significantly improve your experience.
1. Server Location
Proximity matters. Connect to a VPN server geographically closer to your actual location for faster speeds. Distance increases latency. Experiment with different server locations within your region to find the fastest one.
2. VPN Protocol Selection
Different VPN protocols offer varying levels of speed and security. IKEv2 is often a good choice for mobile devices due to its speed and stability. WireGuard is another modern protocol known for its efficiency. Experiment to see which protocol works best for your network conditions.
3. Network Conditions
Your underlying network speed is a limiting factor. A slow Wi-Fi or cellular connection will bottleneck your VPN performance. Try switching between Wi-Fi and cellular to see if there’s an improvement. Consider upgrading your internet plan if possible.
4. App Settings
Many VPN apps allow you to adjust settings like data encryption levels. Lowering the encryption level can sometimes improve speed, but this may compromise security. Find a balance that suits your needs. Close unnecessary background apps to free up resources for your VPN.
The post Secure Your Mobile Life: A Comprehensive Guide on How to Connect to VPN on Your Phone appeared first on gadget.apola.co.
]]>The post Secure Your Data and Protect Your Privacy: A Checklist of What to Do Before Selling or Trading in Your Phone appeared first on gadget.apola.co.
]]>This comprehensive checklist will cover essential procedures applicable to both Android and iOS devices, ensuring a universal approach to data security. We will explore best practices for backing up your valuable data, performing a thorough factory reset to erase all personal information, removing SIM and memory cards, and understanding the intricacies of remote device management features. By following these steps diligently before selling or trading in your phone, you can proactively mitigate potential security breaches and safeguard your privacy in an increasingly interconnected world. Prioritize the protection of your digital footprint – it’s an investment in your peace of mind.
Backing Up Your Data: A Comprehensive Guide
Prior to selling or trading in your phone, it is imperative to create a comprehensive backup of your data. This will ensure that you retain access to your important information and can seamlessly transfer it to a new device.
Methods for Data Backup
Several methods are available for backing up your data, including:
- Cloud-based backup: Utilizing services such as Google Drive (for Android) or iCloud (for iOS) to store your data securely in the cloud.
- Local backup to a computer: Connecting your phone to a computer via USB and using software like iTunes (for iOS) or the phone manufacturer’s software to create a local backup.
- Third-party backup apps: Employing dedicated backup applications available on the app store to create a backup of your data.
Data to Include in Your Backup
Ensure your backup includes the following data categories:
- Contacts
- Photos and Videos
- Text Messages
- Call History
- App Data (where supported)
- Documents
Verify the backup’s integrity before proceeding with the next steps. This confirms the successful preservation of your important information.
Removing Your Google Account and Other Linked Accounts
Prior to selling or trading in your phone, it is imperative to remove all associated accounts. This measure safeguards your personal data and prevents unauthorized access to your information.
Steps to Remove Your Google Account:
- Navigate to the Settings menu on your phone.
- Locate the Accounts or Users & Accounts section. The exact wording may vary depending on your device’s operating system.
- Select your Google account from the list.
- Tap the Remove account option. You may be prompted to confirm your decision.
Removing Other Linked Accounts:
Repeat the process outlined above for any other accounts linked to your device, such as:
- Email accounts (e.g., Yahoo, Outlook)
- Social media accounts (e.g., Facebook, Twitter)
- Cloud storage accounts (e.g., Dropbox, OneDrive)
Ensure that each account is fully removed from the device to prevent any residual data from being accessible to the new owner.
Erasing Personal Data: Factory Resetting Your Phone

Performing a factory reset is crucial to ensure your personal data is completely removed from your phone before selling or trading it in. This process restores the phone to its original factory settings, effectively wiping all user data.
Steps to Perform a Factory Reset (General Guide):
- Back up your data (as outlined in the “Backing Up Your Data” section).
- Go to your phone’s Settings menu.
- Find the “General Management” or “System” section (the exact wording may vary depending on your phone’s manufacturer and operating system).
- Look for the “Reset” option.
- Select “Factory Data Reset.”
- Carefully review the information presented, as this process will erase all data.
- Confirm your decision by tapping “Reset” or “Erase Everything.”
- You may be prompted to enter your PIN, pattern, or password.
- Allow the process to complete. The phone will restart automatically.
Important Considerations:
- The exact location of the “Factory Data Reset” option may vary depending on your phone model and operating system version. Consult your phone’s user manual if needed.
- After the factory reset, your phone will be like new. You will need to set it up again as if it were a brand new device.
- Although a factory reset is effective, it’s still recommended to take additional steps, such as removing your Google account and other linked accounts, to further protect your privacy.
Removing SIM Card and Memory Card
Before selling or trading in your phone, it is imperative to remove both the SIM card and any memory cards (such as MicroSD cards). These cards may contain personal information, contacts, photos, videos, and other sensitive data you don’t want to share with the new owner.
Steps to Remove:
- Power off your phone completely.
- Locate the SIM card tray and memory card slot. This location varies depending on the phone model; consult your phone’s manual if necessary.
- Use the SIM eject tool (or a straightened paperclip) to eject the SIM tray.
- Carefully remove the SIM card and any memory cards from their respective slots.
- Store the SIM card and memory card in a safe place.
Important Considerations:
- Ensure the phone is powered off before removing the cards to prevent data corruption.
- Avoid using excessive force when ejecting the SIM tray.
Checking for Any Remaining Personal Information
Even after performing a factory reset, it is crucial to manually inspect your phone for any residual personal data. This step ensures a higher level of data security and prevents accidental exposure of your private information.
Manual Inspection Checklist:
- Photos and Videos: Scrutinize the gallery app, including hidden folders or cloud-synced albums.
- Files: Check the file manager for any documents, PDFs, or other files you might have downloaded or created.
- Notes and Memos: Review any note-taking apps or memo applications for sensitive information.
- Call Logs and Messages: Although usually cleared with a reset, verify that call logs and SMS/MMS message threads are completely gone.
- Installed Apps: Confirm that all third-party applications have been uninstalled. Sometimes, remnants of app data can persist.
By thoroughly reviewing these areas, you can minimize the risk of inadvertently sharing personal information when selling or trading in your device. This proactive approach helps safeguard your privacy.
Unlocking Your Phone (If Applicable)
Before selling or trading in your phone, it’s crucial to determine if it is locked to a specific carrier. A locked phone can only be used with that carrier’s service, potentially limiting its appeal and value to prospective buyers.
Check Your Phone’s Lock Status: Contact your current carrier to inquire about the lock status of your phone. They can typically provide this information based on your account details and the phone’s IMEI number.
Unlocking Process: If your phone is locked, contact your carrier to request an unlock. Carriers often have specific requirements, such as fulfilling your contract obligations or paying off the phone’s balance. Once the requirements are met, the carrier will provide you with an unlock code or remotely unlock the device.
Benefits of Unlocking: Unlocking your phone increases its value and appeal to a wider range of potential buyers, as it allows them to use the phone with any compatible carrier.
Disabling Find My Device Features
Before selling or trading in your phone, it is crucial to disable any “Find My Device” features. These features, while useful for locating a lost or stolen phone, can compromise your privacy and security if left active on a device you no longer possess.
Steps to Disable “Find My Device” (Example for Android):
- Go to your phone’s Settings.
- Navigate to Security or Location (the exact wording may vary depending on your Android version and manufacturer).
- Look for an option like “Find My Device,” “Find My Phone,” or a similar name.
- Toggle the switch to disable the feature. You may be prompted to enter your Google account password for verification.
Steps to Disable “Find My” (Example for iOS):
- Go to Settings, then tap on your name at the top.
- Tap “Find My.”
- Toggle “Share My Location” to off.
- Tap “Find My [Device]” and toggle it off. You may be prompted to enter your Apple ID password.
Important: Ensure that you have completely disabled the feature and that the device is no longer associated with your account.
Cleaning Your Phone and Accessories
Before you finalize the sale or trade-in of your phone, it is prudent to thoroughly clean the device and its accompanying accessories. This not only enhances its aesthetic appeal but also ensures a more professional transaction.
Cleaning the Phone
Use a soft, lint-free cloth to wipe down the screen, back, and sides of the phone. For stubborn smudges or grime, slightly dampen the cloth with distilled water. Avoid using harsh chemicals or abrasive cleaners, as these can damage the screen coating or other components.
Cleaning Accessories
Clean any included accessories such as the charging cable, earbuds, and case. Use a similar method as with the phone, employing a soft cloth and distilled water if needed. Ensure all accessories are completely dry before packaging them with the phone.
Final Inspection
After cleaning, perform a final inspection to ensure all surfaces are free from dust, fingerprints, and debris. A clean phone presents well and demonstrates attention to detail, potentially increasing its perceived value.
Understanding Data Security and Encryption

Data security and encryption are paramount when preparing to sell or trade in your phone. Encryption transforms your data into an unreadable format, protecting it from unauthorized access. Modern smartphones typically employ full-disk encryption by default.
Here’s a brief overview:
- Encryption: Scrambles data, rendering it incomprehensible without the correct decryption key.
- Importance: Protects sensitive information like contacts, messages, photos, and financial data if your device falls into the wrong hands.
- Factory Reset: While a factory reset is crucial, encryption ensures that even after the reset, recovering residual data is significantly more difficult.
Knowing that your data is encrypted adds an extra layer of security, giving you peace of mind as you prepare your phone for its next owner.
Protecting Your Privacy After Selling Your Phone
Even after taking precautions, it’s vital to remain vigilant about your privacy after selling your phone. While a factory reset and account removal significantly reduce risk, they aren’t foolproof. Here’s how to stay protected:
- Monitor Your Accounts: Keep a close eye on your bank accounts, social media profiles, and email for any unusual activity. Enable two-factor authentication wherever possible.
- Beware of Phishing Scams: Be cautious of phishing attempts that might try to exploit your past association with the phone.
- Update Passwords: Consider updating passwords for your most important accounts, especially those previously logged in on the device.
- Report Potential Identity Theft: If you suspect your identity has been compromised, report it to the appropriate authorities immediately.
- Regularly Review Credit Reports: Checking your credit report helps identify any fraudulent activities early on.
Staying proactive and informed is crucial in safeguarding your personal information in the digital age, even after parting ways with your device.
The post Secure Your Data and Protect Your Privacy: A Checklist of What to Do Before Selling or Trading in Your Phone appeared first on gadget.apola.co.
]]>The post Understanding the Risks and Precautions: How to Root Your Android Device Safely and Effectively appeared first on gadget.apola.co.
]]>This article delves into the intricate world of Android rooting, providing a comprehensive overview of the inherent risks involved and outlining essential precautions to mitigate them. We will explore potential security vulnerabilities, warranty implications, and the possibility of bricking your device. Moreover, we will provide a step-by-step guide on how to root your Android device safely and effectively, empowering you to make informed decisions and navigate the process with confidence. By understanding these risks and precautions, users can leverage the power of rooting responsibly and maximize the potential of their Android devices.
What is Rooting and Why Do People Do It?
Rooting is the process of gaining privileged control (known as “root access”) over an Android device. Think of it as unlocking the administrator privileges on your smartphone or tablet, similar to “jailbreaking” an iPhone. This grants you the ability to modify system files, install custom ROMs, remove pre-installed apps (bloatware), and access advanced settings that are normally restricted by the manufacturer.
People choose to root their Android devices for a variety of reasons, including:
- Customization: Rooting allows users to personalize their device’s interface, functionality, and performance beyond the limitations set by the manufacturer.
- Performance Enhancement: Users can overclock the processor, optimize memory usage, and remove resource-intensive bloatware to improve device speed and battery life.
- Access to Advanced Features: Rooting unlocks access to features and applications that require root access, such as custom kernels, advanced backup solutions, and system-level tweaks.
- Installing Custom ROMs: Custom ROMs offer alternative operating systems with enhanced features, performance improvements, and updated Android versions that may not be available from the manufacturer.
Potential Risks of Rooting Your Android Device
Rooting your Android device, while offering enhanced customization and control, carries significant risks that users should carefully consider before proceeding.
Warranty Voidance
Most manufacturers explicitly state that rooting voids the device’s warranty. If any hardware or software issues arise post-rooting, you may be ineligible for official support or repairs.
Bricking Your Device
A primary concern is the possibility of “bricking” your device, rendering it unusable. This can occur due to incorrect rooting procedures, incompatible software, or interrupted processes. A bricked device may not power on or function at all.
Security Vulnerabilities
Rooting can expose your device to increased security threats. With root access, malicious apps gain deeper system privileges, potentially compromising your personal data and device security. Careful app selection and security measures are crucial.
Software Instability
Rooting can lead to software instability, including app crashes, system errors, and boot loops. This is often due to compatibility issues with custom ROMs or modifications made to the system software.
Over-the-Air (OTA) Update Issues
Rooted devices may encounter difficulties receiving and installing official OTA updates. Custom ROMs or modifications can interfere with the update process, potentially requiring manual flashing or alternative update methods.
Benefits of Rooting Your Android Device
Rooting your Android device offers several potential advantages, providing users with greater control and customization options. While it’s important to weigh these benefits against the risks, many users find the increased functionality worthwhile.
- Enhanced Customization: Rooting allows you to install custom ROMs and kernels, significantly altering the appearance and functionality of your device’s operating system.
- Improved Performance: By removing bloatware (pre-installed apps) and optimizing system settings, you can potentially improve your device’s speed and battery life.
- Access to Advanced Features: Rooting grants access to features and apps that are otherwise restricted by the manufacturer or carrier.
- Full Control Over Your Device: You gain complete control over system files and settings, enabling you to modify and customize your device to your specific needs.
- Bypass Restrictions: Rooting allows you to bypass carrier and manufacturer restrictions, such as tethering limits and app installation limitations.
Ultimately, the benefits of rooting depend on your individual needs and technical expertise. However, for users seeking greater control and customization, rooting can unlock a wide range of possibilities.
Essential Steps to Take Before Rooting

Before embarking on the rooting process, meticulous preparation is crucial to minimize risks and ensure a smooth experience. Neglecting these preliminary steps can lead to complications, including data loss or a bricked device.
Checking Device Compatibility
Verify that your specific Android device model and operating system version are compatible with the intended rooting method. Incompatible methods can cause severe damage. Consult reliable online resources or forums dedicated to Android rooting for device-specific information.
Gathering Necessary Files and Tools
Identify and download all the required files, such as the appropriate rooting software, USB drivers for your device, and any custom recovery images (e.g., TWRP or ClockworkMod). Ensure these files are from trusted sources to avoid malware or corrupted software.
Enabling USB Debugging
Enable USB debugging on your Android device. This option is usually found within the Developer Options menu in the device’s settings. To unlock Developer Options, typically you must repeatedly tap on the “Build Number” option (usually found under “About Phone”) until a message confirms developer mode has been enabled. After enabling, find and enable USB Debugging.
Choosing the Right Rooting Method for Your Device
Selecting the appropriate rooting method for your Android device is crucial for a successful and safe process. Several methods exist, each with its own set of advantages and disadvantages. Understanding these differences is essential.
Common Rooting Methods
- One-Click Rooting Tools: These are user-friendly applications designed to simplify the rooting process. However, their compatibility can be limited to specific devices and Android versions. Examples include KingRoot and iRoot.
- Custom Recovery Flashing: This method involves installing a custom recovery image (e.g., TWRP) and then flashing a rooting package (e.g., Magisk) through the recovery interface. This approach offers more control and is generally considered safer.
- ADB and Fastboot Commands: This is a more advanced method that requires using the Android Debug Bridge (ADB) and Fastboot tools to manually flash necessary files. It provides the most control but also carries a higher risk of bricking your device if not performed correctly.
Factors to Consider
When choosing a rooting method, consider your device model, Android version, technical expertise, and the level of risk you are willing to accept. Research thoroughly to ensure compatibility and follow instructions carefully.
Backing Up Your Android Device Before Rooting
Prior to initiating the rooting process, creating a comprehensive backup of your Android device is an absolutely essential precaution. Rooting inherently carries a risk of data loss or device malfunction, making a recent and complete backup critical for data recovery.
Why Back Up?
The rooting process can sometimes go awry, potentially leading to a factory reset, which erases all data on your device. A backup ensures that you can restore your device to its previous state, mitigating potential data loss.
What to Back Up:
- Contacts: Save to your Google account or export as a vCard file.
- Photos and Videos: Copy to your computer or upload to a cloud storage service (e.g., Google Photos, Dropbox).
- Apps and App Data: Use a dedicated backup app (e.g., Titanium Backup if you already have root access, or Helium for non-rooted devices).
- SMS Messages: Utilize a backup app specifically designed for SMS data.
- Call Logs: Back up using a dedicated call log backup app.
- System Settings: Some apps can back up system settings, which can be helpful for restoring a familiar user experience.
- Important Files: Manually copy any other important documents, files, or media to a safe location.
Backup Methods:
You can back up your device using various methods, including:
- Cloud Backup: Utilizing services like Google Drive or other cloud storage options.
- Local Backup: Copying files to your computer via USB.
- Dedicated Backup Apps: Using specialized apps designed for backing up Android devices.
Detailed Guide on How to Root Android Safely
Rooting an Android device requires careful execution. Before commencing, ensure you have a reliable rooting tool compatible with your device’s model and Android version. Common tools include Magisk, SuperSU, and KingRoot; however, thoroughly research the tool’s reputation and security.
Here’s a general outline:
- Enable Developer Options: Navigate to “Settings” -> “About Phone” and tap “Build Number” seven times.
- Enable USB Debugging: Go to “Settings” -> “Developer Options” and enable “USB Debugging.”
- Unlock Bootloader (If Required): This step varies significantly by device manufacturer. Research the specific process for your device. This step may void your warranty.
- Flash the Rooting Tool: Use a computer and the Android Debug Bridge (ADB) to flash the chosen rooting tool onto your device. This often involves booting your device into bootloader mode.
- Verify Root Access: After flashing, use a root checker app from the Google Play Store to confirm successful rooting.
Disclaimer: Proceed at your own risk. Incorrectly following these steps can brick your device.
Troubleshooting Common Rooting Problems
Rooting, while beneficial, can sometimes lead to complications. This section addresses common issues encountered during the rooting process and provides potential solutions.
Device Not Recognized
Problem: Your computer doesn’t detect your Android device.
Solution: Ensure USB debugging is enabled in Developer Options. Install the correct USB drivers for your device. Try a different USB cable or port.
Rooting Process Stuck or Failed
Problem: The rooting process hangs or terminates prematurely.
Solution: Verify you’re using the correct rooting method for your device model and Android version. Double-check that all prerequisites (e.g., bootloader unlocking) are met. Restart your device and computer and try again. Consider using a different rooting tool.
Boot Loop
Problem: Your device gets stuck in a loop, repeatedly restarting.
Solution: Try booting into recovery mode and wiping the cache partition. If that doesn’t work, you may need to restore a previous backup or flash the original firmware.
No Root Access After Rooting
Problem: After following the rooting process, you still don’t have root access.
Solution: Ensure that SuperSU or Magisk Manager is installed correctly and up to date. Some devices might require additional steps to gain full root access. Verify root using a root checker application.
Verifying Successful Root Access
After completing the rooting process, it is essential to verify that root access has been successfully granted to your Android device. This confirmation ensures that the rooting procedure was executed correctly and that you can now leverage the benefits of a rooted device.
Methods for Verification
Several methods can be employed to verify root access:
- Root Checker Applications: Download and install a root checker application from the Google Play Store. These apps are designed to quickly assess your device’s root status.
- Terminal Emulator Commands: Use a terminal emulator application and execute the command “su”. If root access is granted, the command prompt will change to indicate root privileges (e.g., a ‘#’ symbol).
- Root-Requiring Applications: Install and run an application that requires root access. If the application functions correctly and requests root permissions, it indicates successful rooting.
A successful verification will confirm that your device is properly rooted and that you can proceed with installing custom ROMs, modifying system files, and enjoying other root-enabled functionalities. If verification fails, revisit the rooting process and troubleshooting steps to identify and resolve any potential issues.
Managing Root Access and Permissions
Once your Android device is rooted, it’s crucial to understand how to effectively manage root access and permissions. This ensures the security and stability of your system.
Root access management is primarily handled by a “superuser” application, such as Magisk or SuperSU. These apps act as gatekeepers, controlling which applications are granted root privileges.
When an application requests root access, the superuser app will prompt you with a request. You can then choose to grant or deny this request. It is highly recommended to carefully review each request and only grant root access to applications that you trust and understand. Granting root access to untrusted applications can compromise your device’s security.
Here are some key considerations for managing root access:
- Grant root access sparingly: Only grant root access to applications that genuinely need it.
- Monitor root access requests: Regularly review which applications have been granted root access.
- Revoke unnecessary access: If an application no longer requires root access, revoke it.
- Keep your superuser app updated: Ensure your superuser app is up-to-date to benefit from the latest security patches and features.
The post Understanding the Risks and Precautions: How to Root Your Android Device Safely and Effectively appeared first on gadget.apola.co.
]]>The post Safeguarding Your Digital Life: A Complete Guide on How to Back Up Your iPhone Effectively appeared first on gadget.apola.co.
]]>This comprehensive guide, “Safeguarding Your Digital Life: A Complete Guide on How to Back Up Your iPhone Effectively,” is designed to equip you with the knowledge and tools necessary to protect your iPhone data. We will explore various backup methods, including iCloud backups, computer-based backups using iTunes or Finder, and third-party backup solutions. This guide provides step-by-step instructions, best practices, and troubleshooting tips, ensuring that you can confidently and effectively create secure backups of your iPhone, providing peace of mind knowing your data is safe and secure.
Why Backing Up Your iPhone is Crucial
Backing up your iPhone is an essential practice for safeguarding your valuable data. Your iPhone contains a wealth of personal information, including contacts, photos, videos, messages, notes, and app data. Without a recent backup, this data is at risk of being lost due to various unforeseen circumstances.
Here’s why regular backups are non-negotiable:
- Data Loss Prevention: Accidents happen. Whether it’s physical damage, theft, or a software glitch, a backup ensures you can recover your data.
- Seamless Device Upgrades: When upgrading to a new iPhone or restoring your current device, a backup allows you to transfer your data effortlessly.
- Software Issues: If you encounter iOS problems requiring a device reset, a backup is crucial for restoring your iPhone to its previous state.
- Peace of Mind: Knowing your data is safely backed up provides peace of mind in the face of potential data loss scenarios.
In essence, an iPhone backup serves as a safety net, protecting your digital life from unexpected events.
Choosing Your Backup Method: iCloud vs. Computer
When it comes to backing up your iPhone, you have two primary methods to consider: iCloud and backing up to a computer using Finder (macOS Catalina and later) or iTunes (older macOS versions and Windows). Each method offers distinct advantages and disadvantages, influencing which is the most suitable for your needs.
iCloud Backup
iCloud offers the convenience of automatic, wireless backups. Your data is stored securely in the cloud, accessible from anywhere with an internet connection. However, iCloud provides only 5GB of free storage; exceeding this limit requires purchasing additional storage.
Computer Backup (Finder/iTunes)
Backing up to your computer, on the other hand, stores your backup locally. This method is generally faster, especially for large backups, and it doesn’t rely on internet connectivity. Furthermore, it circumvents the storage limitations associated with free iCloud accounts. The trade-off is the need for a physical connection to your computer and the responsibility of managing the backup file’s security.
Backing Up to iCloud: A Step-by-Step Guide
iCloud offers a convenient and automated way to back up your iPhone’s data wirelessly. Here’s a simple guide to get you started:
- Connect to Wi-Fi: Ensure your iPhone is connected to a stable Wi-Fi network.
- Access Settings: Open the “Settings” app on your iPhone.
- Navigate to iCloud: Tap on your name at the top, then select “iCloud.”
- Initiate Backup: Scroll down and tap “iCloud Backup.”
- Enable iCloud Backup: Toggle the “iCloud Backup” switch to the “on” position.
- Back Up Now: Tap “Back Up Now” to start the backup process immediately. Ensure your device remains connected to Wi-Fi until the backup is complete.
Note: Make sure you have sufficient iCloud storage available for the backup. You can manage your storage in the iCloud settings.
Backing Up to Your Computer Using Finder or iTunes: A Detailed Walkthrough
Backing up your iPhone to a computer provides a secure, local alternative to iCloud. The method varies slightly depending on your computer’s operating system.
For macOS Catalina or Later (Using Finder)
Connect your iPhone to your Mac using a USB cable.
Open Finder. Your iPhone should appear in the sidebar under “Locations”.
Select your iPhone.
Click “Back Up Now”. You can also choose to encrypt your backup.
Click “Manage Backups” to view and manage existing backups.
For Older macOS Versions or Windows (Using iTunes)
Ensure you have the latest version of iTunes installed.
Connect your iPhone to your computer.
Open iTunes. Select your iPhone icon when it appears.
In the “Summary” pane, under “Backups,” select “This computer.”
Click “Back Up Now”. You can encrypt your backup for added security.
To verify the backup, go to iTunes > Preferences > Devices. Your backup should be listed with the date and time.
Important: Keep your USB cable connected during the entire backup process.
Managing Your iCloud Storage for Backups
iCloud storage is often a finite resource, and effectively managing it is critical for ensuring your iPhone backups are successful. Understanding your storage usage and available options is key to avoiding backup interruptions.
Checking Your iCloud Storage
To check your current iCloud storage utilization, navigate to Settings > [Your Name] > iCloud > Manage Storage. This section provides a detailed breakdown of how your storage is being consumed by various apps and services.
Freeing Up iCloud Storage
Several methods can be employed to free up space:
- Delete Unnecessary Backups: Remove older backups of devices you no longer use.
- Disable iCloud Backup for Large Apps: Prevent specific apps with significant data from being backed up to iCloud. Go to Settings > [Your Name] > iCloud > Manage Storage > Backups > [Your Device] and toggle off the apps you don’t need to back up.
- Remove Unwanted Files: Delete photos, videos, and documents from iCloud Drive and other iCloud-integrated apps.
Upgrading Your iCloud Storage
If you consistently run out of storage, consider upgrading your iCloud storage plan. Apple offers various tiers of storage at competitive prices. You can manage your subscription in Settings > [Your Name] > iCloud > Manage Storage > Change Storage Plan.
Encrypting Your iPhone Backups for Enhanced Security
Encrypting your iPhone backups adds a vital layer of security, protecting your sensitive data from unauthorized access. While iCloud backups are encrypted by default, computer backups require manual encryption.
Why Encrypt? Encryption scrambles your data, rendering it unreadable without the correct password. This is crucial if your computer is ever compromised or stolen.
Enabling Encryption for Computer Backups
To encrypt your iPhone backup on your computer:
- Connect your iPhone to your computer.
- Open Finder (macOS Catalina and later) or iTunes (Windows and earlier macOS).
- Select your iPhone.
- In the “General” tab (Finder) or “Summary” tab (iTunes), check the box labeled “Encrypt local backup.”
- You will be prompted to create a strong password. Remember this password! You will need it to restore from this backup. If you lose it, the backup is irretrievable.
Important Considerations: Choose a strong, unique password and store it securely. Apple cannot recover your backup if you forget the encryption password.
Verifying Your Backup: Ensuring Data Integrity
After completing an iPhone backup, it is essential to verify its integrity to ensure your data is safely stored and recoverable. This step confirms that the backup process was successful and that the backup file is not corrupted.
How to Verify Your iCloud Backup:
Go to Settings > [Your Name] > iCloud > Manage Storage > Backups. You should see your device listed with the date and time of the latest backup. If the backup date is recent, it indicates a successful backup.
How to Verify Your Computer Backup:
Using Finder (macOS Catalina or later): Connect your iPhone to your computer and open Finder. Select your iPhone in the sidebar. In the “General” tab, you should see details of your latest backup.
Using iTunes (macOS Mojave or earlier, or Windows): Connect your iPhone and open iTunes. Click on the device icon, then select “Summary.” Under “Backups,” you’ll find information about your latest backup.
If the date and time of the backup are as expected, your backup has likely been created successfully. Regularly verifying your backups ensures you have a reliable copy of your data in case of device failure or data loss.
Restoring Your iPhone from a Backup: A Recovery Guide
This section details the process of restoring your iPhone from a previously created backup. It’s essential to understand this procedure should your device encounter issues requiring a full reset or if you’re transferring data to a new iPhone.
Preparation Before Restoring
Before initiating the restore process, ensure your iPhone is connected to a stable power source and a reliable Wi-Fi network. This prevents interruptions during the restoration, which could potentially lead to data corruption.
Steps to Restore from a Backup
- Erase All Content and Settings: Navigate to Settings > General > Transfer or Reset iPhone > Erase All Content and Settings. This will return your iPhone to its factory settings.
- Follow the Setup Assistant: After the reset, your iPhone will restart and present the Setup Assistant. Follow the on-screen prompts until you reach the Apps & Data screen.
- Choose Restore Option: On the Apps & Data screen, select “Restore from iCloud Backup” or “Restore from Mac or PC,” depending on where your backup is stored.
- Sign In and Select Backup: If restoring from iCloud, sign in with your Apple ID. Then, choose the most recent and relevant backup from the list. If restoring from a computer, connect your iPhone to the computer and follow the prompts in Finder or iTunes.
- Wait for Restoration: The restoration process will begin, and your iPhone will restart. Do not disconnect the power or Wi-Fi during this process.
The restoration time will depend on the size of the backup and the speed of your internet connection. After the process is complete, your iPhone will be restored to the state it was in when the backup was created.
Troubleshooting Common Backup Issues: Solutions and Tips
Encountering issues during the backup process is not uncommon. This section addresses prevalent problems and offers practical solutions.
Common Issues and Resolutions
- Insufficient Storage: Manage your iCloud storage by deleting unnecessary files or upgrading your storage plan. For computer backups, ensure adequate disk space.
- Backup Errors: Restart your iPhone and computer. Ensure both devices are running the latest software versions.
- Slow Backup Speed: A stable and fast Wi-Fi connection is crucial for iCloud backups. For computer backups, use a USB cable and close unnecessary applications.
- Backup Corruption: While rare, corrupted backups can occur. Consider deleting older backups and creating a new one.
- “Not Enough Space on This iPhone” Error: Even when backing up to a computer or iCloud, ensure your iPhone has sufficient free space for temporary files during the backup process.
Tips for Smooth Backups
Periodically check your backup settings and ensure that important data categories (photos, contacts, etc.) are selected for backup. If problems persist, consult Apple Support for specialized assistance.
Best Practices for Regular iPhone Backups
To ensure the safety and accessibility of your iPhone data, adopting consistent backup habits is paramount. Regular backups mitigate data loss risks associated with device damage, theft, or software malfunctions.
Backup Frequency
The frequency of backups depends on your iPhone usage and the importance of your data. Consider these guidelines:
- Daily for critical data: If you frequently create or modify important files (e.g., work documents, important notes), a daily backup is recommended.
- Weekly for moderate usage: For users who primarily use their iPhones for communication and social media, a weekly backup may suffice.
- Monthly for light usage: If your iPhone usage is minimal and your data is not frequently updated, a monthly backup can be adequate.
Automate Your Backups
Enable iCloud Backup to automatically back up your iPhone when it is connected to Wi-Fi, plugged into a power source, and the screen is locked. This ensures consistent backups with minimal effort.
Alternate Backup Methods
In addition to iCloud, consider performing periodic backups to your computer. This provides an additional layer of protection against data loss, especially if you encounter iCloud storage limitations or connectivity issues.
The post Safeguarding Your Digital Life: A Complete Guide on How to Back Up Your iPhone Effectively appeared first on gadget.apola.co.
]]>